One day, quantum computers will become a reality. When that day comes, RSA, Elliptic Curves and many other fundamental cryptographic primitives will become obsolete. Post-Quantum Cryptography offers secure alternatives and we can help you get ready.
Home Technologies Post-Quantum Cryptography
One day, quantum computers will become a reality. When that day comes, RSA, Elliptic Curves and many other fundamental cryptographic primitives will become obsolete. Post-Quantum Cryptography offers secure alternatives and we can help you get ready.
Meet the Holy Grail of cryptography.
Homomorphic encryption is the ultimate cryptographic tool to build more secure cloud computing services that respect everybody's privacy. It allows to confidentialy share data, and the encrypted data can then be processed without ever needing to decrypt or reveal it. Homomorphic encryption is the future, and we can help you get there!
Security by design is not an abstract concept.
Beware of alleged "military grade secure" products. It is one thing to encrypt with AES-256 or to sign with CRYSTALS-Dilithium, doing it correctly is a different kettle of fish.
We can help you build innovative products that require any standard or advanced cryptographic tools, such as elliptic curves, identity-based encryption, post-quantum signatures, e-cash, and many others.
A fresh pair of eyes on your design.
The development of a cryptographic product, from a whiteboard protocol to an industrial grade implementation, is a long and complex process. Our experts will help you avoid common (and less common) pitfalls at any stage of the development.
A french regroupment for post-quantum cryptography.
The RISQ project brings together the french digital security community (academics and industry) in order to prepare the post-quantum revolution. Combining the strong skills of its actors, the RISQ project aims to take part in the development of standards and of new technologies. It also aims to set up processes of migration, so that french industry can be reactive to this technological change. Considering the paramount importance of this project, several major companies decided to get on board even on their own expense.
A crypto-calculus platform for the Cloud.
The principle of cloud computing is to allow users to outsource computation resources to the cloud by allowing a remote service to execute, in their name, some procedures on their private data. While many commercial services are growing fast, to this day, all require the client to place total trust in the service regarding the confidentiality of their data. The aim of CRYPTOCOMP is to develop an efficient cloud-based crypto-calculus platform which, using the latest advances in Fully Homomorphic Encryption, would make it impossible for the cloud service to learn anything whatsoever about the user's data, while still executing the procedures as intended.
Using Fully Homomorphic Encryption in Practice.
The HEAT project will develop advanced cryptographic technologies using Fully Homomorphic Encryption to process sensitive information in ecrypted form, without needing to compromise on the privacy and security of the citizens and organizations that provide the input data.
Europe won’t just follow the post-quantum transition, it will define it.
The migration to post-quantum cryptography (PQC) has become an important topic on the agenda of the EC and member states to protect sensitive information. However, how this migration should happen and, most importantly, what specifically to migrate to, are currently wide open questions. Clear European guidance and standards are needed to permit European IT industry to work on solutions that will be adopted and for all sectors to prepare for and start the migration to PQC.
Building confidence in post-quantum cryptography requires more than strong algorithms.
Focusing on the practical deployment of standardized post-quantum cryptographic (PQC) algorithms, RESQUE emphasizes modular integration, operational agility, and high assurance in real-world applications. As part of the consortium, CryptoExperts leads the effort on side-channel security, targeting one of the most pressing risks in the implementation of PQC algorithms.
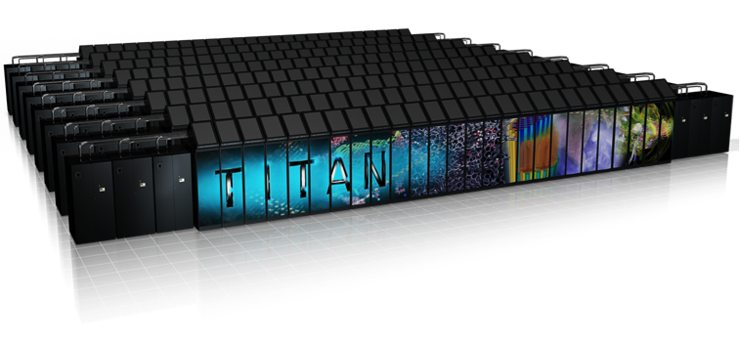
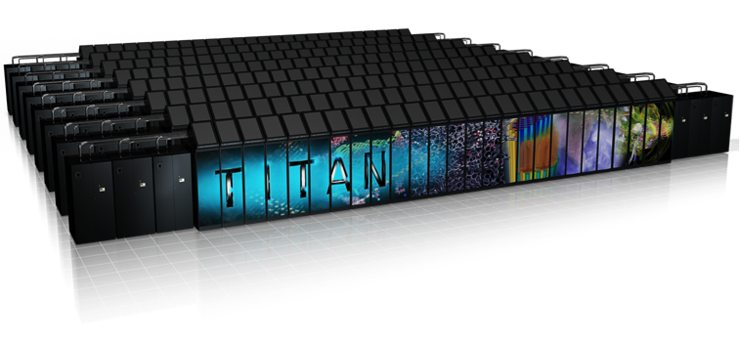
Traditional computers work with bits, simple binary values equal to 0 or 1. Quantum computers on the other hand work with qubits, quantum bits that can be a superposition of both 0 and 1 at the same time. Additional properties, such as the possibility of computing with entangled qubits, allow quantum computer to run specific algorithms that could not run on traditional computers.
A majority of modern cryptographic primitives relies on two problems: integer factorization and discrete logarithm. Both these problems happen to be efficiently solvable using a large enough quantum computer. Luckily, such large quantum computers do not exist yet. Still, most experts agree that at one point in the future, maybe in 5 years, 15 years, or more, they will exist. When that day comes, all security products will need to shift to so-called Post-Quantum Cryptographic primitives.
Many hard problems have been proposed for post-quantum cryptography, but the most trustworthy solutions can be grouped in four families:
CryptoExperts’ team includes experts in each of these specific research topics, so we can tell you exactly which solution best fits your post-quantum cryptographic needs.
NIST launched a competition in 2016 to select the future standards for post-quantum key encapsulation mechanisms, public key encryptions, and signatures. Many candidates were submitted and some of them were already selected for standardization in 2022. In 2023, NIST is launching a new process for the selection of new post-quantum signature candidates. Our team carefully follows and participate to the NIST process, by monitoring the research progresses on the already selected schemes and by proposing a signature scheme candidate.
Our business offer aims at providing flexibility and trust to our customers. That is why we strongly commit on efficiency and security, while considering intellectual property issues and proposing flexible contracting options. In particular, our offer covers:
Contact us and get a precise quotation.
CryptoExperts regroups internationally recognized experts in the field of cryptography with multi-expertise in the different areas of post-quantum cryptography. CryptoExperts was a member of the RISQ project which brought together the French digital security community (academics and industry) to prepare the post-quantum revolution. We are currently taking part to the RESQUE project with several industry leaders to go one step further in the post-quantum transition. Our team maintains up-to-date skills in post-quantum cryptography through the continuous supervision of PhD theses on this particular topic.